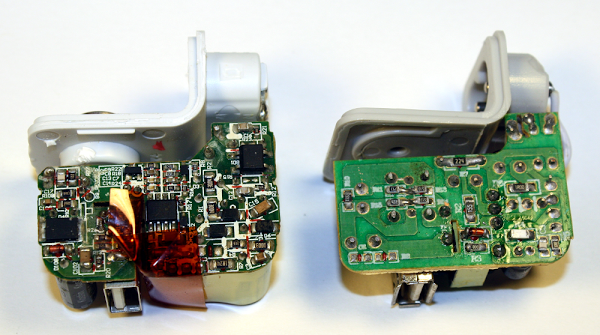
From the outside, the real charger (left) and counterfeit charger (right) are almost identical. If you look very closely, you can spot are a few differences in the text: The counterfeit removed "Designed by Apple in California. Assembled in China" and the manufacturer "Foxlink"[1], probably for legal reasons. (But strangely, the counterfeit still says "TM and © 2010 Apple Inc.") The counterfeit charger displays a bunch of certifications (such as UL) that it doesn't actually have. As you will see below, there is no way it could pass safety testing.
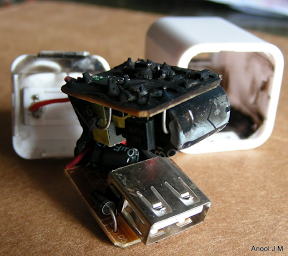
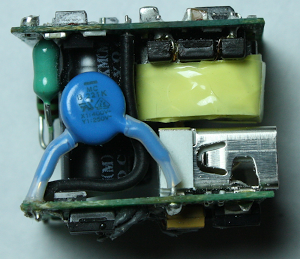
Opening up the chargers reveals big differences between them. The genuine charger on the left is crammed full of components, fitting as much as possible into the case. The counterfeit charger on the right is much simpler with fewer components and much more empty space. The Apple charger uses larger, higher-quality components (in particular the capacitors and the transformer); below you will see that these have a big effect on power quality and safety.
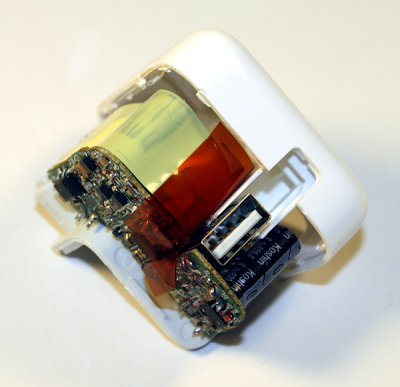
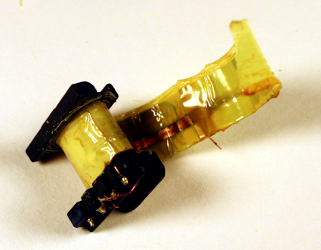
One safety difference is obvious: the Apple charger has much more insulation. The upper (high-voltage) half is wrapped in yellow insulating tape. Some components are encased in shrink tubing, there are plastic insulators between some components, and some wires have extra insulation. The counterfeit charger only has minimal insulation.
The build quality of the Apple charger is much higher. In the counterfeit charger, some components are visibly crooked or askew. While this doesn't affect the circuit electrically, it indicates a lack of care in construction.
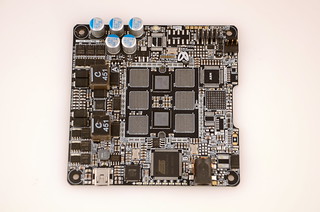
Flipping the boards over reveals that the circuitry of the genuine Apple charger is much more complex than the counterfeit. The Apple board is crammed with tiny surface-mounted components in every available spot. The counterfeit board has a lot of empty space, with just a few components. Note the reddish insulating tape in the lower center of the Apple board, another safety feature of the genuine charger.
How the chargers work
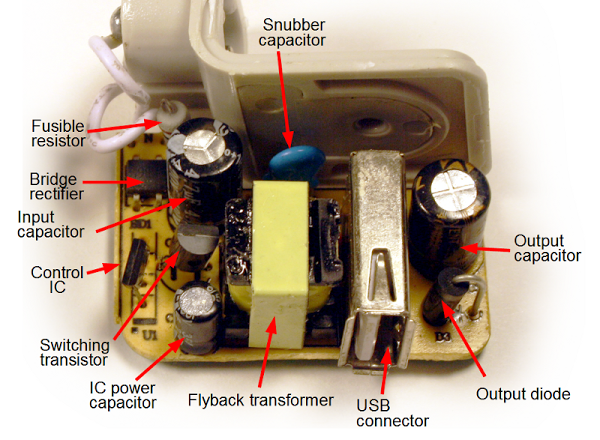
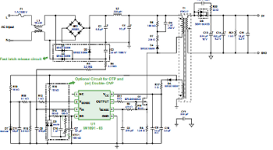
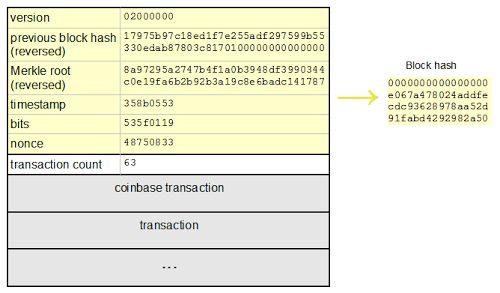
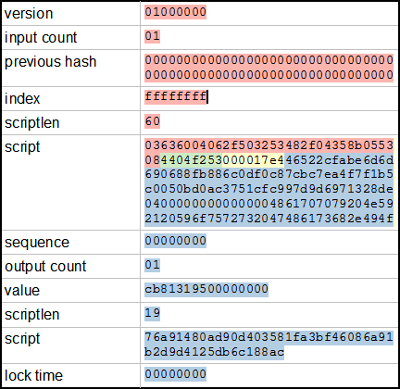
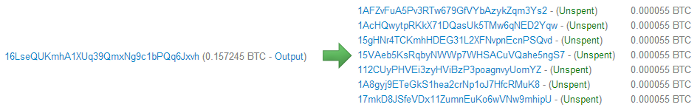
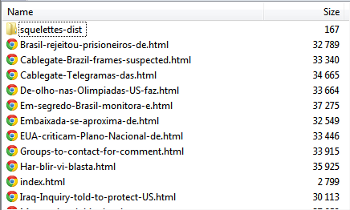
Both the real and counterfeit chargers use similar flyback[2] switching power supply circuits. The switching power supply is the innovation that allows these chargers to be so compact, unlike the heavy "wall warts" powering older consumer electronics. The principle of a switching power supply is the power is switched on and off tens of thousands of times a second, allowing it to provide the exact amount of power required with very little power wasted as heat. In addition, the high frequencies allow the charger to use a small transformer, unlike the bulky transformers used for 60 Hz AC.Since the counterfeit charger is much simpler, it is easier to understand how it works and I'll explain it first in reference to the picture below. The AC power enters through the white wires in the upper left. It passes through a fusible resistor, which acts as a safety fuse. Below this, the bridge rectifier contains four diodes which convert the AC into DC (at about 170 to 340 volts[3]). The input capacitor smooths out this power. The 4-pin control IC[4] monitors the charger and uses the switching transistor to turn the high-voltage DC on and off 41,000 times per second. This chopped DC is fed into the primary winding of the flyback transformer. The transformer converts this to the desired high-current 5 volts. The output diode produces DC, and the output capacitor smooths it out. Finally, the output voltage is available at the USB connector to power your iPad. A few components round out the circuit. A feedback winding on the transformer provides voltage feedback to the control IC. This winding also powers the IC; the IC power capacitor smooths out this power. Finally, the blue snubber[5] capacitor absorbs current spikes when the transistor is switched off.[6]
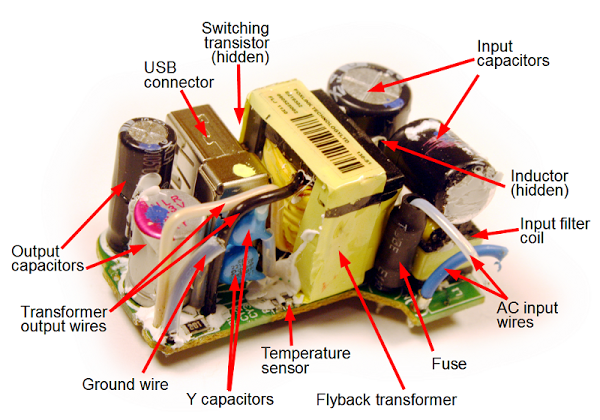
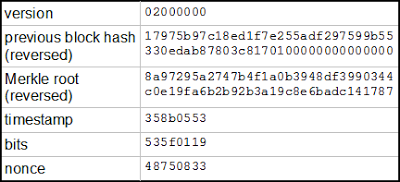
The genuine iPad charger below operates on similar principles, although the circuit is more advanced. The AC input is on the lower right, and goes through a 2A fuse (in black insulation for safety). The primary has much more filtering than in the counterfeit charger with a filter coil (common mode choke), inductor, and two large electrolytic capacitors. This increases the cost, but improves the power quality. On the output side (left), the charger has two filter capacitors, including a high-quality aluminum polymer capacitor (with the magenta stripe). The Y capacitors help reduce interference.[7] The tiny NTC temperature sensor lets the charger shut down if it overheats. (I removed some of the charger's insulation to make the components visible in this photo.)
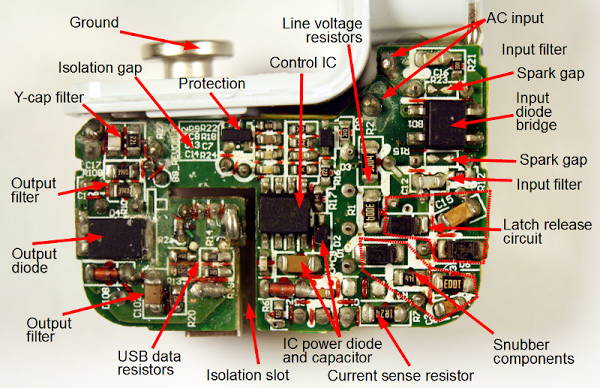
On the other side of the circuit board, things get complicated in the Apple charger. Starting with the AC input in the upper right, the charger includes additional input filters as well as spark gaps.[8] The latch release circuit[9] lets the charger reset quickly from faults. The control IC[10] provides advanced control of the charger under varying conditions. (This IC is much more complex than the control IC in the counterfeit charger.) The current sense resistor lets the IC monitor the current through the transformer and the line voltage resistors let the IC monitor the input voltage (as well as initially powering-up the IC[9]). The protection circuit uses the temperature sensor on the other side of the board to shut down if there is an over-voltage or over-temperature problem. [20]
The secondary side includes some special features for power quality. The Y-capacitor filter works with the Y capacitors to filter out noise. The output filter circuitry is more complex than in the counterfeit. Note that the real charger has a ground connection, unlike the counterfeit charger which has a plastic pin here.[11]
Both chargers use resistors to put special voltages on the USB data lines[12] to indicate the charger type, using Apple's proprietary system (details). (This is why iPads say "Charging is not supported with this accessory" with some chargers.) Through these resistors the genuine charger indicates that it is an Apple 2A charger, while the counterfeit indicates that it is an Apple 1A charger. This shows that the counterfeit is really a 5W charger packaged as a 10W charger.
When looking at these circuits up close, it's easy to forget just how small the components are. The picture below shows one of the surface-mount components (a 0-ohm resistor[13]) from the iPad charger. It is just to the left of Roosevelt's chin on the dime.
Safety, or lack thereof
Safety probably isn't something you think about when you plug in your charger, but it's important. Inside the charger is 170 volts or more with very little separating it from your iPad and you. If something goes wrong, the charger can burn up (below), injure you, or even kill you. Devices such as chargers have strict safety standards[14] - if you get a charger from a reputable manufacturer. If you buy a cheap counterfeit charger, these safety standards are ignored. You can't see the safety risks from the outside, but by taking the chargers apart, I can show you the dangers of the counterfeit.
Creepage and clearance
The UL regulations[14] require safe separation between the high voltage and the low voltage. This is measured by creepage - the distance between them along the circuit board, and clearance - the distance between them through air. The regulations are complex, but in general there should be at least 4mm between high-voltage circuitry and low-voltage circuitry.
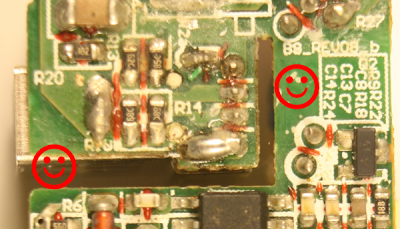
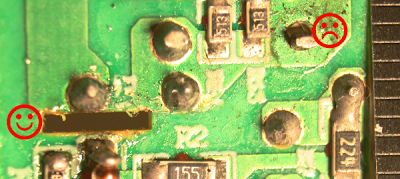
The image above shows how the genuine iPad charger's circuit board separates the high voltage (bottom) from the low voltage (top). The happy face on the right marks an empty region that provides a safety gap between the primary and secondary. (This is a contrast with the rest of the circuit board, which is crammed full of components.) This gap of 5.6mm provides a comfortable safety margin. The happy face on the left marks a slot in the board that separates the low voltage and high voltage. The photo below shows how an insulating fin is built into the case and through this slot to protect the USB connector. Additional reddish-brown insulating tape goes through this slot, and the whole high-voltage section is wrapped in yellow insulating tape. The result is multiple layers of protection.
The creepage distance on the counterfeit charger board below is scary - only 0.6 mm separation between low and high voltage. The sad face on the right shows where a low-voltage trace is nearly touching the high-voltage trace below. (The ruler on the right indicates millimeters.) The board isn't as bad as it could be: the happy face on the left marks a slot cut in the circuit board under the transformer to increase the creepage distance. But overall, this board is unsafe. If you use the charger in a humid bathroom and a drop of water condenses across the 0.6 mm gap, then zap!
Safety in the transformer
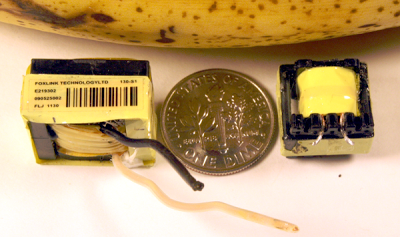
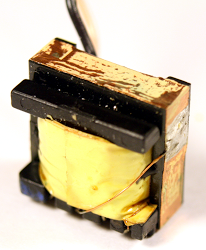
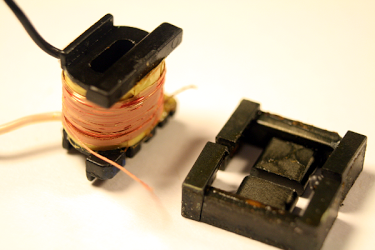
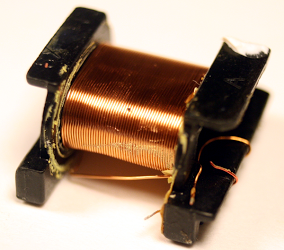
For safety, the high-voltage and low-voltage sides of the charger must be electrically isolated.[15] But obviously the electrical power needs to get through somehow. The flyback transformer accomplishes this task by using magnetic fields to transfer the power without a dangerous direct connection. Because the transformer is a large and relatively expensive component, it is tempting to take safety and quality short cuts here. The genuine transformer (left) is considerably larger than the counterfeit (right), which is a hint of better quality and more power capacity. Disassembling the transformers shows that this is the case.
The key safety requirement of the transformer is to separate the high-voltage windings from the low-voltage secondary winding, and the counterfeit charger fails here. The pictures below show the transformers after removing primary windings and insulating tape, revealing the secondary winding. The wires look similar at first glance, but the the genuine charger (left) has triple-insulated wire while the counterfeit (right) is uninsulated except for a thin varnish. The triple-insulated wire is an important safety feature that keeps the high voltage out even if there is a flaw in the insulating tape and in the wire's insulation. Also note the additional black and white insulation on the wires where they leave the transformer. In the counterfeit charger, the only thing separating the secondary winding from high voltage is the insulating tape. If there is a flaw in the tape or the wires shift too far, then zap!
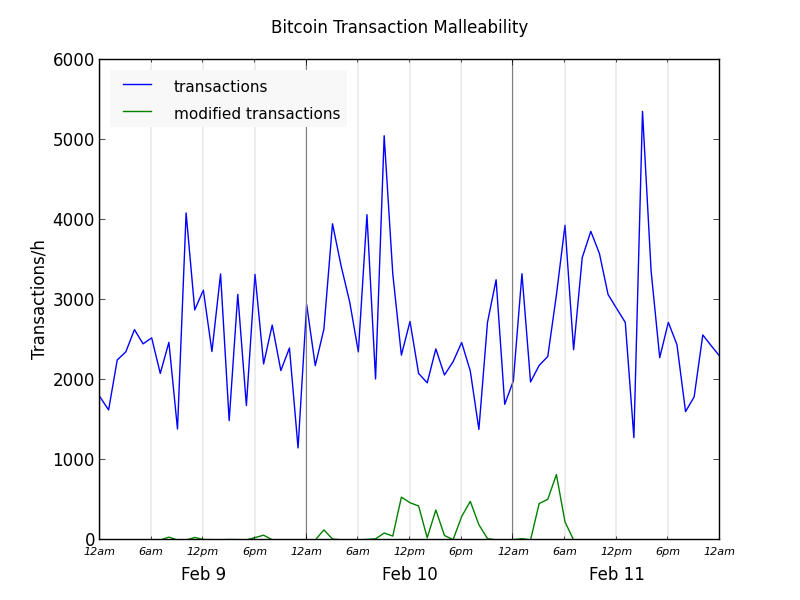
The real charger provides much more power with much less noise
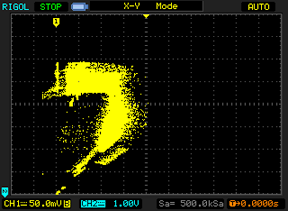
Lab measurements of the output from the chargers shows a couple problems with the counterfeit. First, the counterfeit turns out to provide at most 5.9W, not 10W. Second, the output voltage is extremely noisy and full of spikes.The following voltage-vs-current graphs show the performance of the iPad charger (left) and counterfeit charger (right) under increasing load. The line for the real charger goes much farther to the right, showing that the real charger provides much more current. By my measurements, the real charger provides a maximum of 10.1 watts, while the counterfeit charger provides only 5.9 watts. The consequence is the real charger will charge your iPad almost twice as fast. (For details on these graphs, see my article testing a dozen chargers.) The other thing to note is the line for the Apple charger is smooth and thin, while the counterfeit charger's line is all over the place. This indicates that the power provided by the counterfeit charger is noisy and low quality.
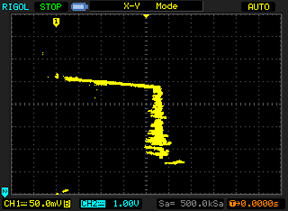
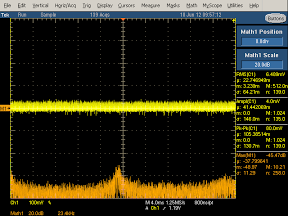
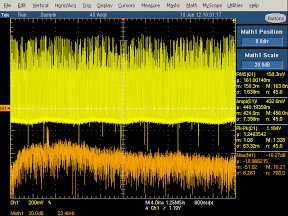
The next pair of graphs shows the power quality. The yellow line shows the voltage. The real charger has a stable yellow thin line, while the counterfeit charger's output has large voltage spikes. (I had to change the scale to get the output to fit on the screen, so the counterfeit charger is actually twice as bad as it appears here.) The bottom of the counterfeit charger's yellow line is wavy, due to 120 Hz ripple appearing in the output voltage.
The orange line shows the frequency spectrum of the output: lower is better, and higher is exponentially worse. The counterfeit spectrum is much higher in general, with a large spike at the switching frequency. This shows that the counterfeit charger's power is worse across the frequency spectrum.
You might wonder if the power quality actually matters. The biggest impact it has is on touchscreen performance. The interference from bad power supplies is known to cause the touchscreen to behave erratically.[16] If your screen malfunctions when plugged into a charger, this is probably the cause.
Inside the real charger's transformer
There's more inside the transformer that you'd expect. This section does a full teardown of the transformer from the genuine charger.
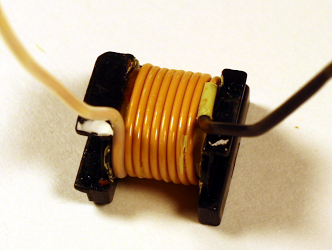
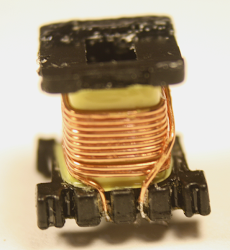
The first photo above shows that underneath the the first layer of yellow insulating tape, a layer of copper foil is attached to the transformer's ferrite core to ground it. Next, removing the ferrite core and more insulation reveals the double-stranded primary winding. The high-voltage input is fed into this winding.
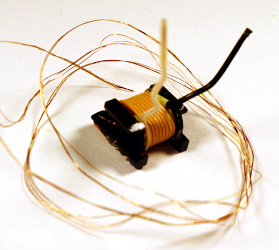
Underneath the primary winding and more insulating tape is the triple-stranded bias winding, which provides feedback and power to the control IC. (In the photo, this winding has been removed and is surrounding the transformer.) After removing more insulating tape, the secondary winding of the transformer is visible. As discussed in the safety section, the secondary winding has triple-insulated wires and extra insulation where the wires leave the transformer. The next layer of insulation (right) contains copper foil. This helps reduce interference.
Finally, the innermost layer of the iPad charger flyback transformer is the second half of the primary winding (above). Splitting the primary winding into two layers is more expensive, but results in a better transformer due to better coupling of the magnetic fields.
In comparison, the transformer of the counterfeit charger is much lower quality. (I haven't included the pictures for reasons of space; click through to see them.) It simply has the bias winding (pic), secondary winding (pic), and primary winding (pic) , separated by insulating tape. Unlike the genuine transformer, the counterfeit saves cost by omitting the copper foil layers. The counterfeit also doesn't use the more expensive split, multi-stranded windings that the genuine charger uses. As discussed earlier, the secondary winding is plain copper wire, not triple-insulated wire, which is a significant safety flaw.
How does the iPad charger compare to the iPhone charger?
The iPad charger is considerably larger than the iPhone charger and provides twice the power. In my detailed iPhone charger teardown I looked at the internals of the iPhone charger. The iPhone charger (below) uses two circuit boards that combine to form a one inch cube, which is impressive engineering. The iPhone and iPad chargers are both flyback switching power supplies, but the feedback mechanisms are very different.[17] Overall, I like the iPhone charger more than the iPad charger from a design standpoint, mainly because of the harder engineering challenge of cramming everything into a much smaller space.
Schematics
In my iPhone charger teardown, I drew up a schematic of the charger, but for the iPad chargers I didn't need to do this. The genuine iPad charger is almost identical[18] to the reference design schematic provided by iWatt. The counterfeit charger is almost identical to the schematic in the DB02A controller datasheet. You can see from the schematics that the genuine charger has a much more complex circuit than the counterfeit. (Click the thumbnails below to get to the datasheets.)
Is the Apple charger worth the price?
Apple's charger is expensive compared to other chargers, but is a high quality product. You should definitely stay away from the cheap counterfeit chargers, as they are low quality and dangerous. Non-Apple name brand chargers are generally good quality according to my tests, with some better than Apple. If you want to get an Apple charger without the high price, the best way I've found is to buy a used one on eBay from a US source. I've bought several for testing, and they have always been genuine.I wrote earlier about Apple's huge profit margins on chargers. Apple has since dropped their charger prices from $29 to $19, which is more reasonable, but looking at the price of similar chargers from other manufacturers and the cost of components, I think Apple has a huge profit margin even at $19.[19]
In any case, the iPad charger is an impressive piece of engineering with a lot of interesting circuitry inside. The counterfeit charger is also impressive in its own way - it's amazing that a charger can be manufactured and sold for such a low price (if you don't care about safety and quality). Overall, you mostly get what you pay for; even if you can't tell from the outside, there are big differences inside the case.
Notes and references
[1] Foxlink (Taiwan), Foxconn (Taiwan), and Flextronics (Singapore) are all manufacturers for Apple with confusingly similar names. Foxconn is the company with controversy over employee treatment; this charger is made by Foxlink, a different company. Interestingly, the chairmen of both companies are brothers and the companies do a lot of business with each other. The companies state that they are entirely independent, though (statement, Foxlink annual report). Foxconn and Flextronics are the world's #1 and #3 largest electronics manufacturing companies according to the MMI top 50 for 2013, while Foxlink is smaller.[2] The chargers uses a flyback design, where the transformer operates "backwards" from how you might expect. When a voltage pulse is sent into the transformer, the output diode blocks the output so there is no output - instead a magnetic field builds up in the transformer. The transformer core has a tiny air gap to help store this field. When the voltage input stops, the magnetic field collapses, transferring power to the output winding. Flyback power supplies are very common for low-wattage power supplies.
[3] You might wonder why the DC voltage inside the power supply is so much higher than the line voltage. The DC voltage is approximately sqrt(2) times the AC voltage, since the diode charges the capacitor to the peak of the AC signal. Thus, the input of 100 to 240 volts AC is converted to a DC voltage of 145 to 345 volts internally. This isn't enough to be officially high voltage but I'll call it high voltage for convenience. According to standards, anything under 50 volts AC or 120 V dc is considered extra-low voltage and is considered safe under normal conditions. But I'll refer to the 5V output as low voltage for convenience.
[4] The counterfeit charger uses a DB02A controller IC. This controller only has four pins and is in a TO-94 (SIP-4) package. (According to the official JEDEC standard, TO-94 is a bolt-like package for large SCRs. It's a puzzle why some companies use TO-94 to describe 4-pin inline packages.) According to the datasheet (Chinese), the chip is for 500mA-1000mA chargers, which explains why the counterfeit charger only produces 5 watts, instead of the 10 watts an iPad charger is supposed to produce. This controller is very inexpensive, available for ¥ 0.35 (about 6 cents).
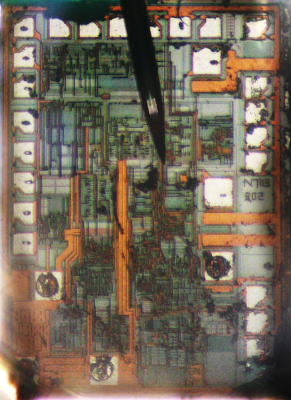
I couldn't find any US chips similar to this chip, even after a lot of searching; it appears to be a Chinese design with datasheets only in Chinese, manufactured by "Fine Made" Shenzhen Fuman Electronics. Since the chip only has four pins, I expected it to be a trivial Ringing Choke Converter (RCC) circuit with just a couple transistors inside the chip - but I cracked it open with Vise-Grips and it turns out to be a fairly complex chip. I took a picture through a microscope of the IC die, which is about 1 mm across. One interesting feature is the many white pads around the outside of the die, which are used to blow fuses to trim various resistances in the chip. I wasn't expecting to see this level of quality and sophistication. The die has the label "N7113 802" at the right; I don't know what this indicates. Three of the four wires connect in the lower left, and the fourth in the lower right.
[5] When a diode or transistor switches, it creates a voltage spike, which can be controlled by a special snubber or clamp circuit. For a lot of information on snubbers and clamps, see Passive Lossless Snubbers for High Frequency PWM Conversion and Switchmode Power Supply Reference Manual.
[6] In the counterfeit charger, the switching transistor is a ALJ 13003 NPN power transistor (datasheet), apparently made by Shenzhen LongJing Microelectronics Co. This transistor is a version of Motorola's MJE 13003 switchmode transistor which was introduced in 1976 (MJE indicates power device in a plastic package). The bridge rectifier is a B6M (datasheet). The output diode is a SR260 Schottky barrier rectifier.
[7] The iPad charger uses special Y-capacitors to bridge the high-voltage and low-voltage sides of the charger. This capacitor helps reduce EMI interference, and is specially designed to avoid any safety hazard. It does, however, pass a tiny amount of electricity - if you feel a tingle from your charger, these capacitors are probably the cause. For more information on X and Y capacitors, see Kemet's presentation and Designing low leakage current power supplies.
[8] The iPad has two spark gaps next to inductor L1 (the input AC common mode choke). I couldn't find a lot of information on this sort of spark gap, but one example of it is an Infineon SMPS design, where similar spark gaps are designed to discharge accumulated charge for a 3KV lightning surge test.
[9] The Apple charger includes a "latch release circuit". If there is a fault, the control IC will shut down the charger until power is removed. However, after unplugging a charger, the input capacitors may store power for many seconds. (You may have seen LEDs remain illuminated for several seconds after unplugging devices.) The latch release circuit ensures that the charger will reset properly even if you plug it back in quickly. It does this by providing a separate diode bridge for the charger's power - this circuit has a much smaller capacitor, so it will power off quickly. (See the schematic for details.) This seems like over-engineering to me, adding extra circuitry for this rare case.
In normal use, by the way, the control IC is powered by the transformer's feedback winding. But if the control IC isn't running, the transformer won't work, leading to a chicken-and-egg situation. The solution is a startup power path where the control IC gets enough power from the AC input to start up, and then switches to the transformer.
[10] The genuine charger uses a complex control chip manufactured by iWatt, the 1691. This chip monitors the input line voltage, the current through the transformer, and the voltage feedback from the transformer. It controls the switching frequency and length of time the power is switched on, with different behavior under no load, low load, and high load, as well as constant monitoring for faults. A detailed presentation on the iW1691 is here. This chip sells for about 30 cents, but I expect Apple gets a better price.
[11] The real charger has a metal ground pin that connects to the power plug, while the counterfeit has a plastic pin. This is one difference between the chargers that is visible externally if you slide the power plug off the charger. Ironically, the US plug doesn't use the ground connection, so this is one safety issue that doesn't make any difference in practice.
[12] Apple uses a proprietary technique for the charger to indicate to the device what kind of charger it is. Different types of Apple chargers use resistances to put different voltages on the USB D+ and D- pins. For details on USB charging protocols, see my earlier references.
[13] While it would be nice to find superconductors inside the charger, unfortunately the zero-ohm resistor is a bit more than 0 ohms. While this resistor may seem pointless, it allows the manufacturers to substitute a resistor later if different transistors require it.
[14] The outside of the charger has the slightly mysterious text: "For use with information technology equipment". This indicates that the charger is covered by the safety standard UL 60950-1, which specifies the various isolation distances required. For a brief overview of isolation distances, see i-Spec Circuit Separation and some of my earlier references.
[15] Only a few special components can safely bridge the gap between the high voltage side of the charger and the low voltage side. The most obvious is the transformer. Y-capacitors can also bridge the primary and secondary side because they are designed not to pass dangerous currents, and not to short out if they fail. Optoisolators use a light signal to provide feedback between the circuits in an iPhone charger, but are not used in the iPad charger.
[16] For an explanation of why the noisy output from cheap chargers messes up touchscreens, see Noise Wars: Projected Capacitance Strikes Back. The article discusses how capacitive touchscreen ICs need to sense pico-Coulombs of charge, which is very difficult when AC noise is present. The article blames touchscreen problems on aftermarket low cost chargers.
[17] The biggest difference between the iPhone charger and the iPad charger is the feedback used to regulate the voltage. The iPhone charger measures the output voltage with a TL431 chip and sends a feedback signal to the control IC via an optoisolator. The iPad charger avoids these components by using primary-side regulation. Instead of measuring the actual output voltage, the iPad control IC looks at the voltage in the feedback winding, which should approximately match the output voltage.
[18] I noticed only a few significant differences between the iPad charger and iWatt's published 1691 charger reference design. This probably means iWatt did most of the design work for Apple.
Comparing the actual charger with the reference design shows a few filtering improvements. The charger has RC snubbers the input bridge rectifier (a rare feature also in the iPhone charger). The charger has an extra diode on the secondary for filtering, as well as a (zener?) diode in the switching transistor drive circuit. The iPad charger uses two Y-capacitors instead of one, and a R/C filter attached to the Y-capacitor on the secondary side. The charger connects line ground to secondary ground through a resistor. The reference design doesn't show the USB data resistors[12].
[19] Some people think that I'm ignoring Apple's cost of designing chargers when figuring their large profit margin. First, if you spend $2 million on design and manufacture 200 million chargers, then design adds only one cent to the cost per charger. Second, iWatt's designers deserve credit for the complex control chip and the reference design, which is most of the design work.
[20] For those interested in the components, the iPad charger's primary diodes (F6w) are 1.5A 60V Schottky Barrier Diodes (datasheet). The "T3" diodes are fast switching diodes (datasheet). The switching transistor is an Infineon SPA04N60C Cool MOS® 650V power transistor (datasheet). The bridge rectifier is a bridge: MB10S CD 0.5A bridge rectifier with high surge capacity (datasheet). The component in the protection circuit that looks like a transistor is a BAV70 dual high-speed switching diode (datasheet). The output diode is a SBR10U45SP5 10A super barrier rectifier (datasheet). The Y capacitors are 220pF 250V. The input capacitors are Samxon 10µFand 4.7µF 400v electrolytics. The output capacitors are a Koshin KLH 820µF 6.3V aluminum electrolytic, and a 820 µF 6.3V X-CON ULR aluminum polymer capacitor (which is more expensive than a regular electrolytic, but filters better because of its lower ESR).